What if someone just around a corner could see what you’re looking at on your computer screen without using a physical or wireless connection and without ever being in your system? It sounds like fiction, and it sounds scary, but it’s based in reality, and it’s been around a long time.
The process is called Van Eck phreaking. Ever heard of it? Not many people have. Van Eck phreaking is the detection of electromagnetic emissions used to spy on what is displayed on a CRT (cathode ray tube) or LCD (liquid-crystal display) monitor as well as the inputs coming from a computer keyboard, a printer, or some other electronic device.
In 1985, Wim van Eck published a paper and the first proof of concept on the idea. He even showed that it could be done from a fairly long distance with a television and $15 worth of equipment.
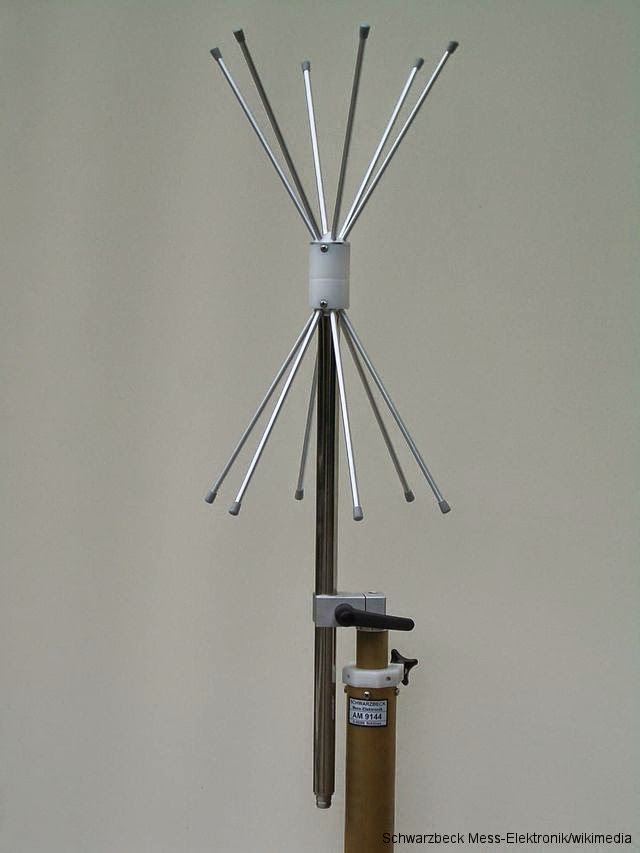
What makes Van Eck phreaking so scary is that it is untraceable. Intrusions are usually done through a computer network, making detection or the ability to trace the action possible. With Van Eck phreaking, that is impossible. The electromagnetic radiation that is emitted from a computer monitor and the cord linking the monitor, or even the keyboard and its cable, can be picked up by an antenna array and displayed on another monitor. All of the information that was on the screen would be displayed as the user sees it, and no one would even know its happening.
Not to fear (maybe), because the National Security Agency (NSA) has been on the case for a long time. The NSA has a codename for this type of spying called TEMPEST. TEMPEST includes information and methods on how to spy on others as well as countermeasures to protect a computer system against this type of spying.
The NSA’s methods are, of course, classified on how to do this type of spying, but the standards for protecting oneself against this spying method are well known and have been released. Not only does TEMPEST address spying dealing with electromagnetic radiation, but it also addresses spying through mechanical vibrations or sounds.
Even though this sounds terrible that someone could be spying on you looking at something on your computer or another electronic device, it is usually not something to worry about. It takes highly specialized equipment to pull off and requires a great deal of effort. There is more of a threat from other types of cyberattacks such as phishing, ransomware, or malware. But for corporations and government entities, this type of intrusion is still a real and dangerous threat.
Many companies, as well as many governments, take this threat seriously and have countermeasures in place. One way they counter a possible attempt is by shielding electromagnetic emission with other metals or encasing a room with metal walls. Another countermeasure involves scrambling the video signal so the signal is much harder to be reproduced.
But the method might be a little easier than what was first previously thought. Research completed in 2004 about the risk of eavesdropping on the electromagnetic signals from flat-panel displays and laptops found that these devices were susceptible to being spied on with the use of equipment that cost less than $2,000.
Check out this older news report video that shows how Van Eck phreaking is done, how clear the image is, and how a password can be stolen.



